What is I.C.E. Certification?

Reduce Risks & Comply with FSG
I.C.E. (Information and Computer Ethics) Certification results from the successful completion of the 10-Rules Program.
10-Rules for Working in the Information Age teaches employees basic concepts in the areas of: Computer Security, Information Privacy, Software Piracy, Social Engineering, Hacking, Netiquette and more. I.C.E. Certification can help to reduce fines and penalites by up to 95%, in keeping with the latest Federal Sentencing Guidelines (FSG).
Common Risks
10 Rules
Here are some areas covered by 10 Rules for Working in the Information Age.
-
 Technology MisuseEthics Resource Center (ERC) concludes that more than 50% of surveyed US workers observed ethical misconduct; including: plagiarism, data fabrication, data misrepresentation, or other forms of dishonesty.
Technology MisuseEthics Resource Center (ERC) concludes that more than 50% of surveyed US workers observed ethical misconduct; including: plagiarism, data fabrication, data misrepresentation, or other forms of dishonesty.
-
 Intellectual PropertyIntellectual property theft in the U.S. has escalated to unparalleled levels, according to the former commander of the U.S. Cyber Command General Keith Alexander. The approximate economic loss to the U.S. amounts to $300 billion per annum.
Intellectual PropertyIntellectual property theft in the U.S. has escalated to unparalleled levels, according to the former commander of the U.S. Cyber Command General Keith Alexander. The approximate economic loss to the U.S. amounts to $300 billion per annum.
-
 Computer SecurityPricewaterhouseCoopers LLP 2014 Cybersecurity Report concludes that organizations do not adequately address employee and insider vulnerabilities, nor do they assess the security practices of third-party partners and supply chains.
Computer SecurityPricewaterhouseCoopers LLP 2014 Cybersecurity Report concludes that organizations do not adequately address employee and insider vulnerabilities, nor do they assess the security practices of third-party partners and supply chains.
-
 Information PrivacyThe International Association of Privacy Professionals states in-house corporate and government privacy respondents indicated that 40 percent had very little funding available to make an impact.
Information PrivacyThe International Association of Privacy Professionals states in-house corporate and government privacy respondents indicated that 40 percent had very little funding available to make an impact.
-
 Software PiracyThe Business Software Alliance states that large and small businesses face serious legal risks because of software piracy. Under the law, a company can be held liable for its employees’ actions.
Software PiracyThe Business Software Alliance states that large and small businesses face serious legal risks because of software piracy. Under the law, a company can be held liable for its employees’ actions.
-
 NetiquetteAccording to Forbes, of all workplace distractions, the Internet is the greatest productivity drain. Sixty four percent of employees visit non-work related websites each day.
NetiquetteAccording to Forbes, of all workplace distractions, the Internet is the greatest productivity drain. Sixty four percent of employees visit non-work related websites each day.
Reasons to have I.C.E. Certification
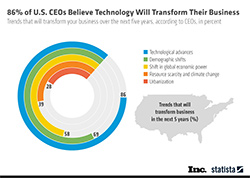
Are my employees using computers inappropriately?
Most probably, yes! The Internet is the greatest productivity drain. 64% of employees visit non-work related websites each day (Forbes), and a new survey—conducted by the American Management Association (AMA)—found that more than 25% of employers have fired workers for misusing e-mail on the job (ComputerWorld). I.C.E. training addresses these potential problems and will help to educate your employees on the proper use of company computers.
Yes! Software piracy can cost your company up to $150,000 in civil fines per infringement and up to $250,000 in criminal fines per infringement. IP infractions can cost your company upto $100,000 per incident in fines and penalties. And, we have not even mentioned bad press. Half of all businesses in America have experienced more than 25 successful social engineering attacks in the past two years, with some having to spend up to $100,000 per incident in cleanup costs (Information Week). I.C.E. training addresses these potential problems and will help to educate your employees on avoiding them.
No! Ignorantia juris non excusat or ignorantia legis neminem excusat (Latin for ignorance of the law does not excuse and ignorance of the law excuses no one) is a legal principle holding that a person who is unaware of a law may not escape liability for violating that law merely because he or she was unaware of its content. I.C.E. Certification demonstrates to courts that you have taken proactive steps to protect your company from inappropriate computer-related actions taken by your employees.
I.C.E. History
Research
Research and developmet of I.C.E. was made possible by grants from the National Science Foundation.Academic
The original program was created as a semester-long course suppliment for computer science and computer engineering departments. Colleges and Universities purchasing the program include: MIT, Stanford, Cornell, Purdue, Darmouth, University of Illinois, and many more.Corporate
10-Rules for Working in the Information Age, a 30 minute online program, was developed for businesses to comply with Federal Sentencing Guidelines and to reduce fines and penalites associated with computer and IT misuse.
© 2022, ILT. All rights reserved. Terms of Use | Privacy Policy